A famous dating website was vandalized, and its 32 million members leaked. The website of the UK’s National Health Service was defaced; so was the website of a U.S. presidential candidate in 2020. Could your company’s site be defaced by competitors, hacktivists, state-sponsored actors, or even those seeking to plant malware onto unsuspecting end users? It’s possible. Fortunately, it’s also preventable.
Website defacement and vandalism is not new. Back in 2002, hackers placed a fake front page and six stories on the front page of USA Today’s website. The New York Times saw its website defaced twice in 2017. Fake material has been placed onto countless websites, including those from the U.S. government’s Federal Depository Library Program and even the U.S. State Department.
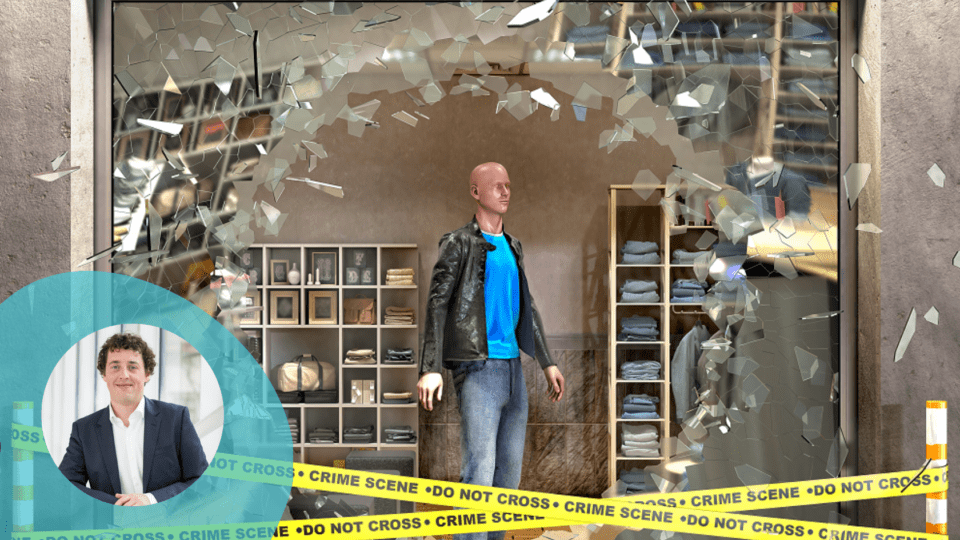
Think of web defacement as virtual graffiti or vandalism, where bad actors deface a website by changing its appearance or content. Sometimes, the hacker might even subvert the website by injecting malicious code that infects customers’ computers or phone with viruses, crypto miners, or to execute phishing scams.
Website defacement can be accomplished by gaining access to the content management system (CMS). Many sites, including those of news media and retailers, are driven almost entirely by a CMS, and if the bad actors can break into that system by stealing credentials, exploiting software vulnerabilities or getting into the network, they can change the displayed content quite easily.
No matter the technical cause, this is serious. CISA, the U.S. Cybersecurity & Infrastructure Security Agency, says that cyberattacks against public-facing websites, regardless of size, are common and may result in website defacement and other forms of vandalism. Such attacks “can gravely damage the reputation of the website and its owner.” For example, says CISA, corporate and personal websites that fall victim to defacement may experience financial loss due to eroded user trust or a decrease in website visitors.
That brings up the question of motivation. Sometimes the defacement is a crime of opportunity: Hackers want to plant malware and they scan high-traffic websites looking for vulnerabilities that will give them access to the front-end web server or the backend content database. Yet at other times, the vandalism deliberately targets a specific government agency, business or nonprofit organization.
As you can see, the motives vary. Perhaps the hackers wish to specifically hurt or embarrass a company. Perhaps they want to plant malware to help them mine cryptocurrency using your computer, or to steal user credentials. Perhaps they are seeking to make a political statement. Perhaps they’re bored or showing off. Perhaps they are looking to gain attention for themselves or their cause. Perhaps it’s a dry run for a state-sponsored entity’s cyberwarfare brigade. Who knows?
At the end of the day, the reasons for the attack shouldn’t matter, at least not to the victim. Leave those psychological analyses and crime forensics to the police or the FBI, while you focus on the real challenges of keeping your corporate IT assets, including your website, safe and secure from hackers and vandals.
Here is a three-pronged approach to preventing, responding to and rebuilding after a website vandalism attack:
First: Plan. Seek to prevent an attack by hardening your defenses, enabling strong encryption and user authentication systems, ensuring there are no exploitable vulnerabilities, and creating comprehensive data backups. Check your software platforms: Have you installed all the patches and fixes? Are you monitoring industry threat notifications for warnings about new vulnerabilities? Are your contractors and employees following the best practices for secure programming and testing? Are your vendors performing at the highest, most secure level, such as by seeking ISO 27001 certification?
To borrow a concept from the airline industry, make sure aircraft materials are not easily flammable, nothing can make sparks and smoking is prohibited near the fuel depot.
Second: Respond. Assume your preventative measures won’t be sufficient to block the attack. If vandals manage to gain access to your systems, it’s essential to detect and react quickly before damage can occur. For detection, monitor logs, look for anomalies and be wary of anything outside the usual. Respond by setting up measures to lock out and ban the attacking actors if vandalism or other breaches occur, while reducing access to prevent further harm, preserve evidence and begin the recovery.
That is, install heat and smoke detectors and automatic sprinklers in case a fire does break out, with lots of red lights and sirens.
Third: Recover. You don’t want to plan for failure, but you should always assume that an attack will succeed. Make sure those backups work. Prepare for contingencies of all sorts. Serve a reduced version of your website or a placeholder until evidence is secured and the system is restored. Have a media response plan in place, and know how to contact the relevant hosting companies, software vendors, customers, partners and law enforcement.
By analogy, that’s why aircraft have drop-down oxygen masks, and why the flight attendants always explain what to do in the event of a water landing, while the airline knows how to contact family members if the unthinkable happens.
Plan. Respond. Recover. Or, like the New York Times or the U.S. State Department, your site might be next on the vandal’s graffiti hitlist.
Sebastian Gierlinger is an experienced developer, team builder and leader. As VP of Engineering at Storyblok, he is committed to providing everything a developer could need when working with a headless CMS. He has more than 10 years of experience in CMS systems security, performance and usability. Outside of work Gierlinger has a passion for organizing community events for developers and is always up for a good cup of coffee.