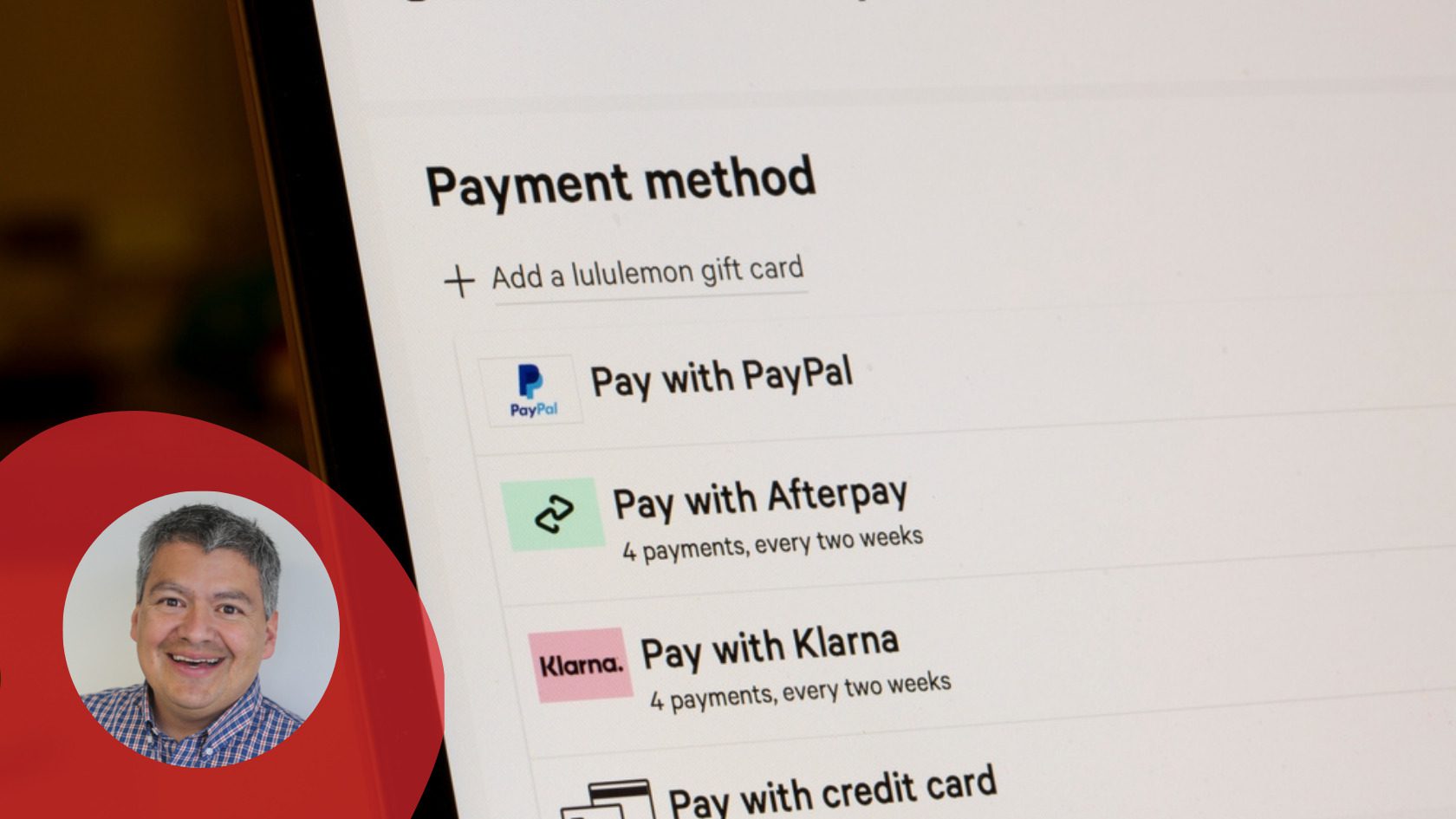
Buy now pay later (BNPL) is one of the largest, fastest-growing and most well-funded segments in the fintech market. According to Accenture, the number of BNPL users in the U.S. has grown by more than 300% per year since 2018, reaching 45 million active users in 2021. But as stand-alone BNPL apps continue to grow, so will the threats against them.
It’s clear this reverse layaway payment model is also here to stay. It’s not hard to understand the appeal. In BNPL, consumers receive the goods or services that they want to buy, but payment is staggered over monthly payments for a certain period of time with no interest. If the purchase amount is not paid off by a certain deadline, then typically the consumer must pay deferred interest plus additional interest until final payoff.
It’s good for consumers, because so long as they pay off the purchase price within the set timeline, they get a no-interest loan to purchase goods immediately that they may have otherwise had to save up to buy. For merchants, it enables them to sell more goods and services without sacrificing revenue, because typically a financial institution or fintech company structures the transaction as a deferred interest loan with the consumer.
But these BNPL apps are extremely appealing to hackers, fraudsters and cybercriminals, because they make it so simple to get credit with simple application processes and minimal (if any) credit checks. There’s a great deal of sensitive data embedded within these apps that cybercriminals can use for fraud, and the apps themselves can be modified and reverse engineered to obtain fraudulent loans. And these two cases just scratch the surface of how cybercriminals can profit from attacking these apps.
BNPL app developers need to ensure that their apps protect end users, and while there are dozens of measures they could potentially take to harden security, here are the top five weaknesses that I see in BNPL apps that must immediately be addressed:
Modified Apps that Enable Synthetic Identity Fraud: BNPL apps are vulnerable to attacks that use fake accounts, emulators and other automated systems to buy products and services for which they have no intention of paying. For instance, a cybercriminal could create 100 fake accounts to buy a variety of laptop computers. They make a single payment before they close the account and then resell the laptops elsewhere for a hefty profit. To protect against this kind of fraud, the BNPL app must be prevented from running on emulators, and it must block debuggers, tools like Magisk that can root a device to obtain higher privileges and other automated environments.
Overlay and Keylogging Attacks: In these attacks, a fake or even hidden screen is rendered above the mobile BNPL app’s screen or entry field, which enables keylogging malware to capture passwords and other sensitive information that can be used to execute an account takeover. Preventing this attack requires the app to sense overlays and shut down when detected and to block keyloggers.
Vulnerable BNPL Data and APIs: BNPL apps, like most mobile apps, depend heavily on backend services such as payment processing to which they connect via application programming interfaces, better known as APIs. And within the apps, the addresses of these backend services, along with keys and tokens that provide authorization to connect, are all hard coded into the app. Additionally, like any fintech app, BNPL mobile apps contain a wealth of sensitive and valuable data.
This data absolutely must be protected with encryption, both at rest and in transit, along with jailbreak and root prevention to prevent hackers from gaining elevated privileges that could enable them to access this data.
Trojans: Using a BNPL mobile app is so easy and credit is so available that consumers are often lulled into a false sense of safety on which cybercriminals can prey. If hackers can reverse engineer the app, they can create a trojan that looks and feels like the real thing, but instead steals sensitive information, enables account takeovers and wreaks all kinds of other havoc.
To prevent cybercriminals from transforming a BNPL mobile app into a malware trojan, developers need to incorporate measures that prevent reverse engineering, mobile app tampering, repackaging and resigning.
Hacking and Fraudster Research: Nearly all BNPL exploits and fraud are based on the ability of a hacker to reverse engineer the mobile app so they can understand its primary workflows, such as purchases and account creation. Once they have this information, fraudsters can leverage it to initiate all kinds of schemes and attacks. To prevent this kind of malicious research, the BNPL app code must be properly obfuscated, and dynamic binary instrumentation toolkits should be blocked so they cannot be abused.
BNPL mobile apps are experiencing exponential growth, and the benefits they can provide to merchants and consumers are many. But if they are not properly secured, public breaches and hacks will damage consumer confidence. By securing these BNPL apps against common threats, fintech companies and retailers can help ensure continued growth and adoption for this exciting new payment model.
Tom Tovar is CEO and Co-creator of Appdome, a no-code mobile security solutions platform. Prior to Appdome, Tovar served as Executive Chairman of Badgeville, an enterprise engagement platform acquired by CallidusCloud; CEO of Nominum, a DNS security and services provider that was acquired by Akamai; and Chief Compliance Officer and VP of Corporate Development and Legal Affairs at Netscreen Technologies. He began his career as a corporate and securities attorney with Cooley Godward LLP. Tovar holds a JD from Stanford Law School and a BBA in finance and accounting from the University of Houston.